You’ve Been Hacked! Lessons Learned from a Cyber Breach
A Practice Handles a Hack, and a PA Considers the Insurance Implications
By Hillel Kuttler
April 10, 2020
The sun hadn’t yet risen on Thursday, January 16, when the office manager of a family practice in Austin, Texas, unlocked the door and turned on her computer. The practice’s PA, nurse practitioner, and two physicians hadn’t yet walked in, and it would be an hour before the first patient arrived. Like every other morning, the manager was getting the practice ready for the day ahead. The computer awoke, but something was awry.
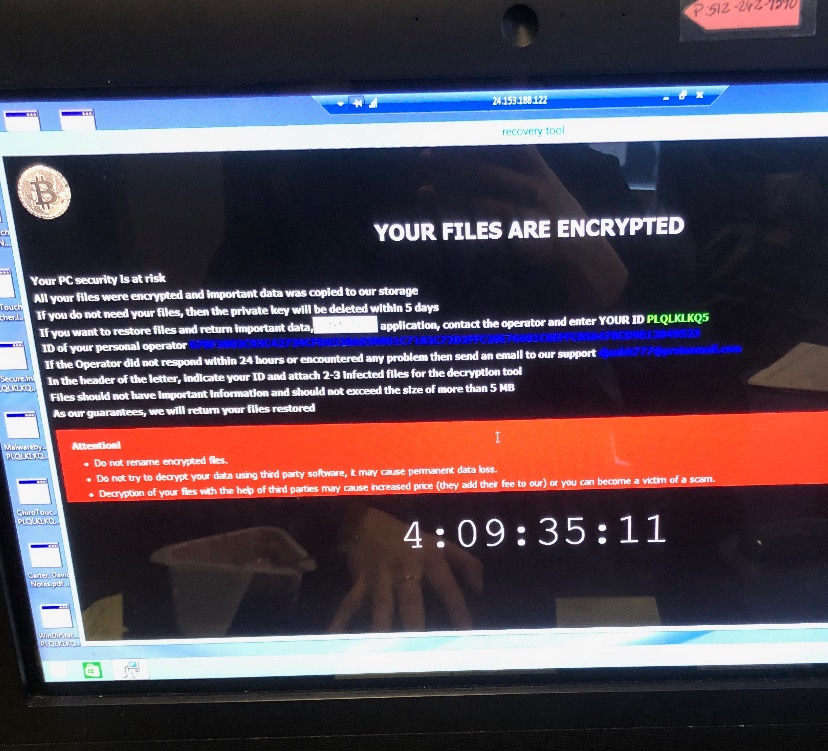
YOUR FILES ARE ENCRYPTED
Atop a black screen screamed an all-capitals headline in white: YOUR FILES ARE ENCRYPTED. A bitcoin logo in the top-left corner hinted at a financial scam, but the 13 lines of text didn’t explicitly say so.
It was a hack. The practice’s scheduling software and patients’ electronic medical records were now inaccessible, held hostage by someone, somewhere. The computer system was rendered useless, at least temporarily. The next three workdays proceeded as if the staff had traveled backward in time, forced to rely on pen, paper, and carbon copies for notetaking and communicating, including writing prescriptions and laboratory orders. The intake process slowed. Labs had to fax test results and hospitals had to fax records.
Fortunately, two of the days’ schedules had been printed before the hack. Even then, those patients had to be called and told to bring any medications to their appointments; that way, refills could be ordered if necessary. During appointments, patients were asked to remind the practitioner of their medical histories and recent surgeries.
$12,000 ransom and $10,000 in attorney fees
Only the following Tuesday did the practice return to normal. By then, the hack had cost the practice $22,000: $12,000 in the ransom paid in bitcoin to the hackers and $10,000 for consultations with the practice’s lawyers. Less calculable was the disruption in running a medical office, the wasted hours by practitioners and other staff, the time spent by the practice’s information-technology (IT) specialist in dealing with the hack and preventing its recurrence, the post-crisis inputting electronically of the handwritten information, the stress.
The hack and its aftermath were a “crazy” time, said the practice’s PA, E.M. (The PA is identified in this article by initials due to her employer’s concern about patients’ potential reactions to the cyberattack and the ongoing forensic report.)

Financial fallout could have been worse
Still, the practice dodged a bullet. Patients’ data appear not to have been compromised. The financial fallout could have been far greater. Will Sullivan, a vice president at CM&F Group, an AAPA-endorsed insurance provider, stated that 60% of small- and medium-sized companies, including those in healthcare, go out of business within six months of a cyber breach.
Data breaches cost healthcare organizations worldwide an average of $380 for each patient’s lost or stolen record – more than double the $141 average for records across all industries – according to a 2017 report published by the Michigan-based Ponemon Institute and sponsored by IBM Security.
[Malpractice Insurance Basics]
The higher expense comes in three areas, said Sullivan: greater legal costs, the cost of notifying governmental agencies, and the cost to alert every patient.
The third area could have gotten extremely expensive in the case of the Texas practice, because it would have had to notify each of its nearly 11,000 patients of the breach. That would have necessitated mailings and, possibly, hiring credit-report companies to monitor any untoward use of patients’ identities.
Patient data more valuable
According to Sullivan and CM&F’s website, someone’s health record is 10–20 times more valuable to hackers than credit card information because the record contains the person’s name, address, birthdate, Social Security number, diagnoses, and billing information, all of which can be used in identity theft.
“Healthcare is one of the most frequent targets of cyber-crime because they have what on the black market would be considered the golden ticket,” Sullivan said.
The Texas practice’s patients were not told what happened because a post-breach forensics investigation found that the hackers had temporarily locked the medical records rather than stolen them, E.M. said.
Complicating the insurance situation was that the practice’s physicians each have cyber-liability policies, but the NP and E.M. do not – and the NP is the sole owner of the practice. That led E.M. to contact AAPA in the breach’s aftermath. E.M. wondered whether she might, by default, be covered by her supervising physician’s cyber-liability policy. But she was concerned that by not independently having a cyber-liability policy, she was exposed at least partially to any damages.
“It raises the question for PAs: I don’t own the practice, but do I have to buy cyber-liability insurance? How much liability do I have to our patients?” she said.
Non-practice owner not liable for hacking costs
Sullivan thinks that in such a situation, a medical professional who doesn’t own the practice wouldn’t be liable for hacking-related costs.
As it turned out, the Texas practice didn’t take the hit for the $12,000 ransom paid to the hackers. While the NP’s medical liability policy didn’t include cyber-related coverage, her policy with another company covered theft. The practice’s losses fell into that category, it turned out, because its server was in the office, rather than being cloud-based. The practice did have to pay the legal fees.
“I couldn’t believe it!” E.M. said of her employer’s relatively good fortune. “We thought the clinic would be out 22 grand.”
E.M. turned sober at what could have been damaging for herself.
“The conundrum would’ve been if I, the PA, was the [practice’s] owner and not covered for cyber-theft. I have my own medical-liability [coverage], but it doesn’t have a cyber component,” she said. “It raised questions I’m not aware of that we should know about.”
She’s not alone. A survey conducted by the American Medical Association and the consultancy Accenture of 1,300 physicians in 2017 found that 83% have experienced cyberattacks at their clinical practice, 55% are “very concerned” or “extremely concerned” about a future attack, and 74% are most concerned by an attack’s interrupting the practice’s functioning. Nine percent of the attacks physicians experienced held patients’ data for ransom.
The findings “suggest a strong need for improved cybersecurity education for physicians,” the survey concluded.
Cybersecurity policies coming
CM&F has not offered cyber-liability insurance, but this spring plans to introduce such policies for medical providers. The policies will cover up to $1 million in each of the following areas: security and privacy liability, security-breach response coverage, and cyber-extortion coverage.
Those policies, Sullivan said, will cover an entire practice. In E.M.’s case, the four medical professionals and the rest of the staff wouldn’t have to purchase separate cyber-liability policies through Sullivan’s company.
As to her agreeing to share the January episode with AAPA through this article, E.M. said she is glad to assist “in any way I can to help protect PAs in the future.”
Hillel Kuttler is a freelance writer and editor. Contact him at [email protected].
You May Also Like
PA Portfolio
Malpractice Insurance Basics
Business Ownership and Independent Contracting
Thank you for reading AAPA’s News Central
You have 2 articles left this month. Create a free account to read more stories, or become a member for more access to exclusive benefits! Already have an account? Log in.